Is Your Link Removal Team Incompetent
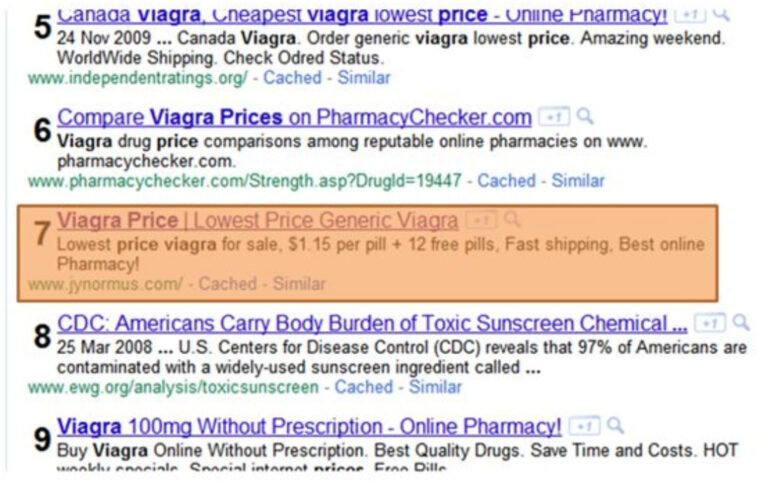
In the recent spate of Google’s anti “easy” link updates, also known as Penguin , link removal has become an essential part of SEO. There are many reasons to remove a link: There may be other reasons, but the above are my top five. How Do I Identify Bad Links? To be honest there isn’t …